| Listing 1 - 3 of 3 |
Sort by
|
Book
ISBN: 0124104193 0124166938 9780124104198 9780124166936 Year: 2014 Publisher: Oxford, [England] ; San Diego, California : Academic Press,
Abstract | Keywords | Export | Availability | Bookmark
 Loading...
Loading...Choose an application
- Reference Manager
- EndNote
- RefWorks (Direct export to RefWorks)
Forensic Document Examination enlightens forensic document examiners, forensic investigators, attorneys, and others using the services of forensic document examiners with basic principles, current trends in the area, and standards and methodologies which were non-existent 20 years ago. Instrumentation has moved beyond the microscope and the magnifying glass to digital cameras, digital microscopes, video spectral comparators, electrostatic detection devices for the development of indented writing on paper, scanners, and software programs like Write-On 2® and Photoshop®. All of this equipment an
Crime laboratories -- Planning. --- Identification cards -- Forgeries -- Identification. --- Legal documents -- Identification. --- Legal documents --- Writing --- Evidence, Documentary --- Social Welfare & Social Work --- Social Sciences --- Criminology, Penology & Juvenile Delinquency --- Identification --- Identification cards --- Crime laboratories --- Identification. --- Forgeries. --- Planning. --- Forensic laboratories --- Forensic sciences laboratories --- Laboratories --- Fake identification cards --- Forged identification cards --- Forgery of identification cards --- Phony identification cards --- Documents, Identification of --- Identification of documents --- Criminal investigation
ISBN: 1281055999 9786611055998 0080478085 1931836515 1932266259 9781932266252 9780080478081 9781931836517 Year: 2002 Publisher: Rockland, MA : Syngress,
Abstract | Keywords | Export | Availability | Bookmark
 Loading...
Loading...Choose an application
- Reference Manager
- EndNote
- RefWorks (Direct export to RefWorks)
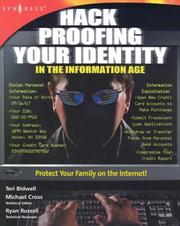
Identity-theft is the fastest growing crime in America, affecting approximately 900,000 new victims each year. Protect your assets and personal information online with this comprehensive guide.Hack Proofing Your Identity will provide readers with hands-on instruction for how to secure their personal information on multiple devices. It will include simple measures as well as advanced techniques gleaned from experts in the field who have years of experience with identity theft and fraud. This book will also provide readers with instruction for identifying cyber-crime and the different
Computer security. --- Identification cards --- Internet fraud. --- Computer crimes. --- Impostors and imposture. --- Forgeries. --- Computers and crime --- Cyber crimes --- Cybercrimes --- Electronic crimes (Computer crimes) --- Internet crimes --- Charlatans --- Imposters --- Pretenders --- Fake identification cards --- Forged identification cards --- Forgery of identification cards --- Phony identification cards --- Computer privacy --- Computer system security --- Computer systems --- Computers --- Cyber security --- Cybersecurity --- Electronic digital computers --- Security of computer systems --- Security measures --- Protection of computer systems --- Protection --- Crime --- Privacy, Right of --- Computer crimes --- Fraud --- Criminals --- Data protection --- Security systems --- Hacking
Book
ISBN: 2130494382 9782130494386 Year: 1998 Publisher: Paris : PUF - Presses Universitaires de France,
Abstract | Keywords | Export | Availability | Bookmark
 Loading...
Loading...Choose an application
- Reference Manager
- EndNote
- RefWorks (Direct export to RefWorks)
Fraude --- Faux --- Crimes et criminels --- Forgery --- Identification cards --- Reproduction of money, documents, etc --- Counterfeits and counterfeiting --- Forgeries --- -Reproduction of money, documents, etc --- 343.92 --- Legal documents --- Money --- Cards, Identification --- Credentials (Identification cards) --- I.D. cards --- ID cards --- Identity cards --- IDs (Identification cards) --- Fraud --- Offenses against property --- Swindlers and swindling --- Coining, Illicit --- Counterfeit money --- Counterfeiting of money --- Illicit coining --- Counterfeits and counterfeiting. --- Forgery. --- Reproduction of money, documents, etc. --- Forgeries. --- Fake identification cards --- Forged identification cards --- Forgery of identification cards --- Phony identification cards --- Identification cards - Forgeries --- FRAUDES INFORMATIQUES --- CRIMINOLOGIE --- DROIT PENAL --- FAUX DOCUMENTS --- FRAUDE --- CARTES --- BANQUE --- IDENTITE
| Listing 1 - 3 of 3 |
Sort by
|

 Search
Search Feedback
Feedback About
About Help
Help News
News