| Listing 1 - 10 of 41 | << page >> |
Sort by
|
Book
Year: 1957 Publisher: [Reading] : University of Reading. Dept. of Agricultural Chemistry, Faculty of Agriculture and Horticulture,
Abstract | Keywords | Export | Availability | Bookmark
 Loading...
Loading...Choose an application
- Reference Manager
- EndNote
- RefWorks (Direct export to RefWorks)
Digital
ISBN: 9781597495547 1597495549 Year: 2010 Publisher: Burlington, MA Syngress
Abstract | Keywords | Export | Availability | Bookmark
 Loading...
Loading...Choose an application
- Reference Manager
- EndNote
- RefWorks (Direct export to RefWorks)
Do you need to keep up with the latest hacks, attacks, and exploits effecting USB technology? Then you need Seven Deadliest USB Attacks. This book pinpoints the most dangerous hacks and exploits specific to USB, laying out the anatomy of these attacks including how to make your system more secure. You will discover the best ways to defend against these vicious hacks with step-by-step instruction and learn techniques to make your computer and network impenetrable. Attacks detailed in this book include: USB Hacksaw USB Switchblade USB Based Virus/Malicous Code Launch USB Device Overflow RAMdump Pod Slurping Social Engineering and USB Technology Knowledge is power, find out about the most dominant attacks currently waging war on computers and networks globally Discover the best ways to defend against these vicious attacks; step-by-step instruction shows you how Institute countermeasures, don't be caught defenseless again, learn techniques to make your computer and network impenetrable.
Book
ISBN: 1283477173 9786613477170 1430239220 1430239212 Year: 2011 Publisher: Berkeley, CA : Apress : Imprint: Apress,
Abstract | Keywords | Export | Availability | Bookmark
 Loading...
Loading...Choose an application
- Reference Manager
- EndNote
- RefWorks (Direct export to RefWorks)
In today’s turbulent technological environment, it’s becoming increasingly crucial for companies to know about the principle of least privilege. These organizations often have the best security software money can buy, with equally developed policies with which to execute them, but they fail to take into account the weakest link in their implementation: human nature. Despite all other efforts, people can sway from what they should be doing. Preventing Good People from doing Bad Things drives that concept home to business executives, auditors, and IT professionals alike. Instead of going through the step-by-step process of implementation, the book points out the implications of allowing users to run with unlimited administrator rights, discusses the technology and supplementation of Microsoft’s Group Policy, and dives into the different environments least privilege affects, such as Unix and Linux servers, and databases. Readers will learn ways to protect virtual environments, how to secure multi-tenancy for the cloud, information about least privilege for applications, and how compliance enters the picture. The book also discusses the cost advantages of preventing good people from doing bad things. Each of the chapters emphasizes the need auditors, business executives, and IT professionals all have for least privilege, and discuss in detail the tensions and solutions it takes to implement this principle. Each chapter includes data from technology analysts including Forrester, Gartner, IDC, and Burton, along with analyst and industry expert quotations.
Computer hackers. --- Computer networks --- Computer security. --- Data protection. --- Computer security --- Hackers --- Data protection --- Commerce --- Electrical & Computer Engineering --- Management --- Business & Economics --- Engineering & Applied Sciences --- Management Theory --- Telecommunications --- Local Commerce --- Security measures. --- Security measures --- Information technology --- Business --- Data processing --- Data governance --- Data regulation --- Personal data protection --- Protection, Data --- Computer privacy --- Computer system security --- Computer systems --- Computers --- Cyber security --- Cybersecurity --- Electronic digital computers --- Security of computer systems --- Protection of computer systems --- Protection --- Business. --- Management science. --- Business and Management. --- Business and Management, general. --- Quantitative business analysis --- Problem solving --- Operations research --- Statistical decision --- Trade --- Economics --- Industrial management --- Electronic data processing --- Security systems --- Hacking
Book
ISBN: 1282738267 9786612738265 1597495549 1597495530 9781597495547 9781597495530 Year: 2010 Publisher: Burlington, MA : Syngress,
Abstract | Keywords | Export | Availability | Bookmark
 Loading...
Loading...Choose an application
- Reference Manager
- EndNote
- RefWorks (Direct export to RefWorks)
Do you need to keep up with the latest hacks, attacks, and exploits effecting USB technology? Then you need Seven Deadliest USB Attacks. This book pinpoints the most dangerous hacks and exploits specific to USB, laying out the anatomy of these attacks including how to make your system more secure. You will discover the best ways to defend against these vicious hacks with step-by-step instruction and learn techniques to make your computer and network impenetrable. Attacks detailed in this book include: USB HacksawUSB SwitchbladeUSB Based Virus/Malicous Co
Computer networks - Security measures. --- Computer security. --- Computer security --- Computer networks --- Engineering & Applied Sciences --- Electrical & Computer Engineering --- Telecommunications --- Computer Science --- Security measures --- Security measures. --- Information Technology --- General and Others --- Computer network security --- Network security, Computer --- Security of computer networks --- Computer privacy --- Computer system security --- Computer systems --- Computers --- Cyber security --- Cybersecurity --- Electronic digital computers --- Protection of computer systems --- Security of computer systems --- Data protection --- Security systems --- Hacking --- Protection
Book
ISBN: 1442223448 9781442223448 9781299636712 1299636713 144222343X 9781442223431 9781442223431 Year: 2013 Publisher: Lanham : Rowman & Littlefield Publishers, Inc.,
Abstract | Keywords | Export | Availability | Bookmark
 Loading...
Loading...Choose an application
- Reference Manager
- EndNote
- RefWorks (Direct export to RefWorks)
While there is plenty of literature on California's history, topography, and attractions, The Beholden State: California's Lost Promise and How to Recapture It is the first book examining in rigorous detail how a place seen just a generation ago as the dynamic engine of the American future could, through bad policy ideas, find itself with among the highest unemployment rates and poorest educational outcomes in the country
California --- Alta California (Province) --- CA --- Cal. --- Cali. --- Calif. --- Californias (Province) --- CF --- Chia-chou --- Departamento de Californias --- Kʻaellipʻonia --- Kʻaellipʻonia-ju --- Kʻaellipʻoniaju --- Kalifornii --- Kalifornii︠a︡ --- Kalifornija --- Ḳalifornyah --- Ḳalifornye --- Kālīfūrniyā --- Kaliphornia --- Karapōnia --- Kariforunia --- Kariforunia-shū --- Medinat Ḳalifornyah --- Politeia tēs Kaliphornias --- Provincia de Californias --- Shtat Kalifornii︠a︡ --- State of California --- Upper California --- Πολιτεία της Καλιφόρνιας --- Καλιφόρνια --- Штат Каліфорнія --- Калифорния --- Калифорнија --- Калифорнии --- Каліфорнія --- קאליפארניע --- קליפורניה --- מדינת קליפורניה --- كاليفورنيا --- カリフォルニア --- カリフォルニア州 --- 캘리포니아 --- 캘리포니아 주 --- 캘리포니아주 --- Economic conditions --- Social conditions --- Politics and government
Book
ISBN: 3030873005 3030872998 Year: 2021 Publisher: Cham, Switzerland : Palgrave Macmillan,
Abstract | Keywords | Export | Availability | Bookmark
 Loading...
Loading...Choose an application
- Reference Manager
- EndNote
- RefWorks (Direct export to RefWorks)
Entrepreneurship. --- Leadership. --- New business enterprises --- Management. --- Ability --- Command of troops --- Followership --- Entrepreneur --- Intrapreneur --- Capitalism --- Business incubators
Digital
ISBN: 9781430239222 Year: 2011 Publisher: Berkeley, CA Apress
Abstract | Keywords | Export | Availability | Bookmark
 Loading...
Loading...Choose an application
- Reference Manager
- EndNote
- RefWorks (Direct export to RefWorks)
Digital
ISBN: 9783030873004 9783030873011 9783030872991 Year: 2021 Publisher: Cham Springer International Publishing, Imprint: Palgrave Macmillan
Abstract | Keywords | Export | Availability | Bookmark
 Loading...
Loading...Choose an application
- Reference Manager
- EndNote
- RefWorks (Direct export to RefWorks)
This book sits at the intersection of two lines of inquiry of critical importance to management researchers-what are the contributory factors to building an entrepreneurial company, and what is senior leadership's role in this process? Inherently cross-disciplinary, it adopts a behavioral perspective and proposes a research model delineating how various strategic leadership variables influence a firm's exhibition of entrepreneurial behaviors, captured by the entrepreneurial orientation (EO) construct. While EO research touches briefly on the role of the CEO senior leadership consideration, the field lacks an integrated perspective on how senior leadership decisions enable or constrain EO. To address this gap, the author proposes resource allocation decisions as the central mechanism through which a set of strategic leadership variables causally influence EO. He argues for the superiority of a behavioral view of EO and of strategic leadership, which stands in contrast to the attitudinal perspective on EO and the ex officio perspective on strategic leadership. Opening a rich new stream of inquiry on leadership antecedents to EO, this work will appeal to both entrepreneurship and leadership researchers, unpacking both research gaps and research questions concerning the role of the CEO and top management team, corporate boards, and emerging leadership challenges. Brian S. Anderson is professor at University of Missouri-Kansas City, US. His research centers on strategic entrepreneurship, focusing on causal inference, measurement issues, and Bayesian treatment of the entrepreneurial orientation and strategic entrepreneurial behavior constructs. His research appears in leading entrepreneurship and management journals, and he serves as an associate editor for strategic entrepreneurship for the Journal of Business Venturing and on the editorial board of Entrepreneurship Theory and Practice. He teaches in the areas of analytics, data science, and strategy.
Social psychology --- Business policy --- Organization theory --- Personnel management --- Business management --- ondernemingsstrategieën --- bedrijven --- B2B (business-to-business) --- management --- leidinggeven --- strategisch beleid --- ondernemen
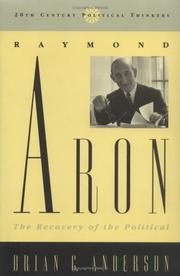
ISBN: 0847687589 Year: 1998 Publisher: Totowa Rowman & Littlefield
Abstract | Keywords | Export | Availability | Bookmark
 Loading...
Loading...Choose an application
- Reference Manager
- EndNote
- RefWorks (Direct export to RefWorks)
Book
Abstract | Keywords | Export | Availability | Bookmark
 Loading...
Loading...Choose an application
- Reference Manager
- EndNote
- RefWorks (Direct export to RefWorks)
Cemeteries --- Church buildings --- Inscriptions --- Registers of births, etc --- Novak, Michael --- Turner County (Ga.) --- Genealogy.
| Listing 1 - 10 of 41 | << page >> |
Sort by
|

 Search
Search Feedback
Feedback About
About Help
Help News
News